Installing KALI Linux in VirtualBox
KALI Linux has generated a great deal of interest. It is one of the premier security toolkits avalable.
KALI Linux is Bad Ass.
What is KALI Linux you ask?
Kali Linux is a security-focused operating system you can run off a CD or USB drive, anywhere.
Kali Linux is packed with software for testing security holes in your network.
Remember: use these powers for good, not for evil. Knowing how to do these things can help you learn to secure your own network, but doing them to someone else is not something we recommend.
It may get you in legal problems if you use these tools on somebody's network without proper authorization and documentation. Get everything in writing if you decide to use it for pen testing!
I will let the folks from www.offensive-security.com explain:
What is Kali Linux ?

Kali Linux is the new generation of the industry-leading BackTrack Linux penetration testing and security auditing Linux distribution. Kali Linux is a complete re-build of BackTrack from the ground up, adhering completely to Debian development standards.
Should I Use Kali Linux?

As the distribution developers, one would likely expect us to recommend that everyone use Kali Linux but the fact of the matter is, that Kali is a Linux distribution specifically geared towards professional penetration testing and security auditing.
Kali Linux Default Passwords

During installation, Kali Linux allows users to configure a password for the root user. However, should you decide to boot the live image instead, the i386, amd64, and ARM images are configured with the default root password – “toor“, without the quotes.
First, download and install VirtualBox. The link is here:
The latest version (4.3.18) is here:
https://www.virtualbox.org/wiki/Downloads
Install VirtualBox and use the default settings if you have not done so.
Download the latest ISO file (1.0.9a) here:
http://www.kali.org/downloads/
Start VirtualBox and create a new VM:
The default RAM allocated is 256 Mb. I bumped that up to 1024 Mb.
VirtualBox then will create a new Virtual Hard drive. Click "Create".
Select the default VDI (VirtualBox Disk Image).
Dynamically allocated drives will use less space, but fixed size will be a bit faster.
Here you can choose the size of the drive. The default (8 Gb) work fine.
Now we have a new VM template. Add the ISO image as an secondary IDE drive here:
Set the PAE bit on in VirtualBox system settings:
Under System Settings, uncheck the VT-x/AMD-v checkbox.
When you start your new VM, a warning box pops up:
And we are at the main boot screen. Select Live (686-pae), Live (686-pae failsafe), Live (forensic mode), Live USB Persistence, Live USB Encrypted Persistence, or Install. I am going to install it on the new VM.
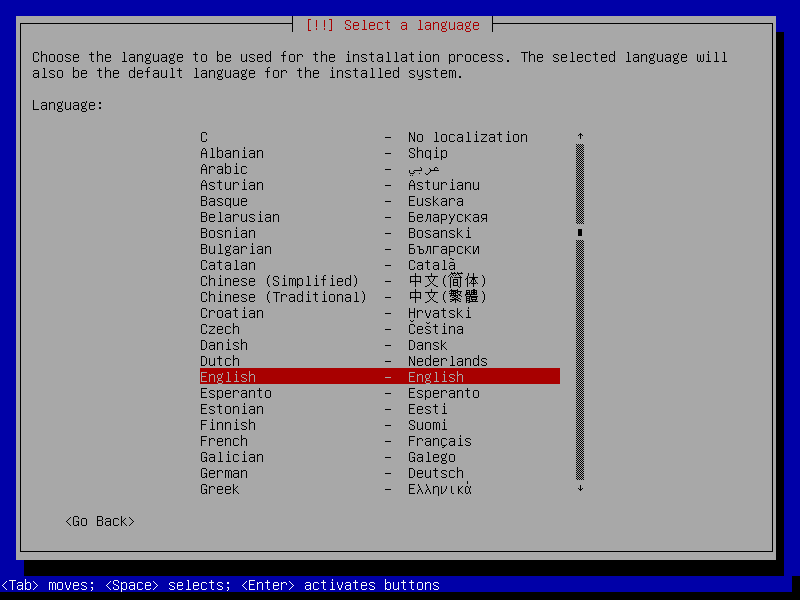
We need to select the default language. I choose English.
Here we are at the standard Debian installer screen with options to configure the keyboard, mount a CD-ROM, load installer components from CD-ROM, change debconf priority, check CD-ROM integrity, save debug logs, execute a shell, or abort installation.
Then we select a time zone we want to use.
KALI then install additional components ala Debian:
Set the host name for your new VM here:
Set your VM's root password here and once again to verify:
And set your timezone here for your region:
Then we partition the disk manually or let the installer do it.
The installer confirms the target disk is the SCSI3 VBOX HARDDISK:
I choose the separate /home, /usr, /var, and /tmp partition.
Format is done, choose write changes to disk.
Yes, I am really really sure. Just do it already.
There are a TON of tools available to pen test almost anything. I will explore these later.
Here is a related article to use KALI for WiFi network pen testing.
There are too many options to list them all here here, but we’re so enamoured with it that we decided to pick a few of our favourite tools — Aircrack, Airbase and ARPspoof– and teach you how they work. We’ll show you how to crack a Wi-Fi password with brute force techniques, create a fake router to trick machines into logging into it, and perform a man-in-the-middle attack to eavesdrop on network communications.